Sometimes nmap does half the work for you. .git on port 80 is all the hint you need.
Machine info
| Name | Dog |
| Platform | HackTheBox |
| OS | Linux |
| Difficulty | Easy |
TL;DR
- Nmap’s
http-gitscript flags an exposed.gitdirectory; a browser extension confirms it gitdumper.pyreconstructs the repository and surfaces the Backdrop CMS settings file with database credentials:root:BackDropJ2024DS2024- The git history reveals an admin email; the DB password also works as the admin panel password
- Backdrop admin access allows installing a malicious module - shell as
www-data sudo -lshowsbee(Backdrop’s CLI) without a password;bee php-evalwithsudogives root
Recon
Nmap
| |
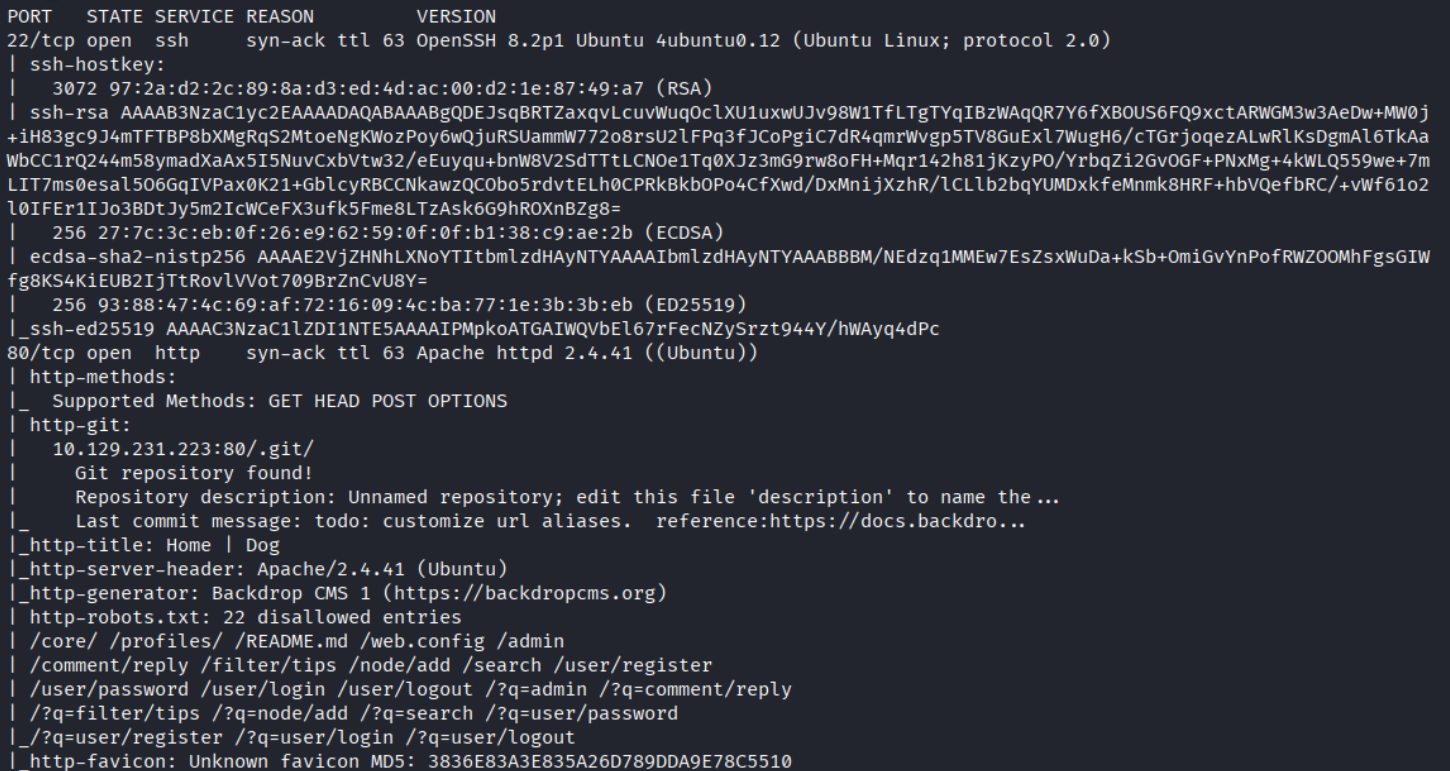
Ports 22 (SSH) and 80 (HTTP, Apache 2.4.41 Ubuntu). The nmap output has two things worth flagging immediately: the http-title is “Home | Dog”, and the http-git NSE script reports a Git repository at /.git/ with a remote pointing to https://gitea.dog.htb/BackDropDevs/dog_development. The robots.txt entries are all Backdrop CMS paths. Framework and source exposure confirmed in one scan.
Enumeration
Exposed .git
The .GIT browser extension catches it too:
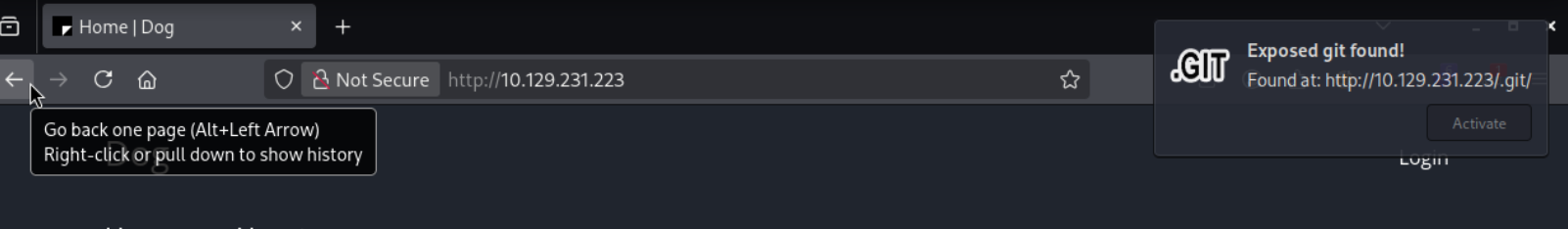
A publicly accessible .git directory means the entire source history is downloadable - including any config files, credentials, or secrets that were ever committed.
Dumping the repository
| |
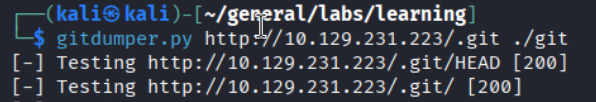
gitdumper.py reconstructs the repository from the exposed object store. Once done, git checkout -- . restores the working tree.
Credentials in settings.php
Digging through the dumped files, the Backdrop CMS settings file contains the database connection string:
| |
Database user root, password BackDropJ2024DS2024. Backdrop also ships helper scripts under core/scripts/ - including password-hash.sh - which become useful if credential reuse doesn’t pan out.
Admin email from git history
| |
Reviewing the commit history surfaces the admin user’s email address. Added dog.htb to /etc/hosts and tried logging into the Backdrop admin panel at /user/login.
Foothold
Backdrop admin access
The database password BackDropJ2024DS2024 works as the admin panel password. Credential reuse between the database and the web application is the single biggest bang-for-buck check after you find any plaintext credential.
Module upload RCE
Backdrop CMS allows admins to install modules by uploading a .zip archive. This is a direct code execution path. Create a minimal malicious module with a PHP backdoor:
| |
Upload via Functionality > Install New Modules, then trigger execution:
| |
RCE confirmed. Set up a netcat listener and send a reverse shell:
| |
Shell as www-data@dog.
Lateral move to user
| |
The database password works here too. User flag captured.
Privilege Escalation
sudo -l
| |
| |
bee is Backdrop’s drush-equivalent CLI tool. Running it without a password as any user means we can use it to execute arbitrary PHP as root.
bee php-eval shell escape
| |
bee accepts a --root path pointing to a Backdrop installation and executes PHP in that context. Since sudo runs the process as root, system() spawns root’s shell.
Root.
Takeaways
- An exposed
.giton a web server is critical severity. The entire source history, including credentials and internal configs, is reconstructable by anyone with a gitdumper script. This is a one-command compromise. - Database credentials get reused everywhere. The same password unlocked the DB connection string, the admin panel, and a system user account. Every credential you find is worth trying against every login surface.
- Backdrop module upload is the same class of bug as Joomla template edit or WordPress plugin install. Any CMS admin panel that can deploy code is an RCE primitive. Enumerate CMS admin access aggressively.
sudoon a CLI tool with eval/exec capabilities is an instant root.bee,drush,wp-cli, and similar tools all have PHP eval or shell-command features. If any of them appear insudo -l, it’s game over.
References
- HackTheBox - Dog
- GitDumper - git-dumper
- GTFOBins - bee
- Lain Kusanagi list (OSCP prep)
